Technical updates to dotdigital

When our customers interact with Dotdigital, they do so using HTTPS. The “S” stands for Secure, and all the data sent and received during that interaction with our platform is encrypted; meaning no one can read it as it passes over networks and the internet.
Over time there have been various protocols used to achieve this secure transmission of data, and more recently, Dotdigital has supported TLS (Transport Layer Security) versions 1.0, 1.1, 1.2, and 1.3.
The time has come for us to turn off support for the older versions of the protocol; these being 1.0 and 1.1. However, we’ll continue to support TLS 1.2 and 1.3 for the foreseeable future.
When will these changes happen?
We are switching off TLS versions 1.0 and 1.1 in two stages. For the first stage, on all of our web applications. And then for the second stage, on our API endpoints. This is to allow enough time, for customers with integrations, to make any necessary changes to their infrastructure.
| System | Description | Change date |
| Dotdigital web applications: 1. Dotdigital 2. Legacy CPaaS products including Campaign Manager and Message Manager 3. Dotdigital CPaaS portal | Where customers connect via their browsers to log in, create content, send campaigns, view reports, and manage their accounts. End consumers of our customers who click on tracked links, landing pages, unsubscribe, and preference centers. | September 16, 2020 |
| API endpoints: 1. api.dotmailer.com and regional variants r1/r2/r3-api.dotmailer.com 2. api.comapi.com | Where customer servers connect to consume dotdigital API services | July 14, 2021 |
After these dates, connections from systems that do not support TLS 1.2 or higher will fail, and services will appear unavailable.
Why the change?
TLS 1.0 and 1.1 have been considered legacy protocols for some time now, as they do not offer the same level of security as their more modern counterparts with organizations such as NIST and the NCSC advising against their use.
At Dotdigital, we’ve managed the security vs usability trade-offs by disabling the weaker parts (ciphers) of the legacy protocols, and mitigating against known exploits – all while continuously monitoring usage across our infrastructure. Using those metrics, we’re now in an excellent position to disable the legacy protocols on our web applications without impacting our customers (with legacy TLS usage making up 0.05% of all connections). This is predominately down to internet browsers now auto-updating, and in more recent versions of the browsers, only enabling TLS 1.2 and 1.3 by default.
Across our API endpoints, we still see a higher percentage of legacy TLS usage. This is down to the server software on which our customers build their integrations tending not to have the same auto-update functionality – requiring somebody to apply the updates on the server manually.
We’re advising all customers using our APIs to check with their IT administrator contacts to ensure that their integrations and software can support TLS 1.2 or 1.3. We will continue to analyze the data and will attempt to contact those customers still using legacy protocols where possible.
Questions?
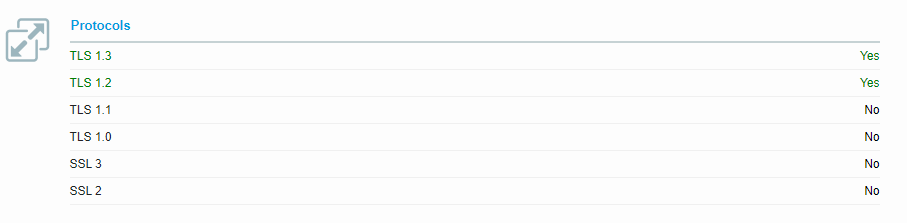
If you have any questions please contact security@dotdigital.com You can check your own browser’s TLS support by visiting Qualys SSL Labs, and confirming that TLS 1.2 and 1.3 say “Yes”